ClearSky Team has identified a targeted Russian cyber campaign against Ukraine utilizing two
novel malware strains, BadPaw and MeowMeow.
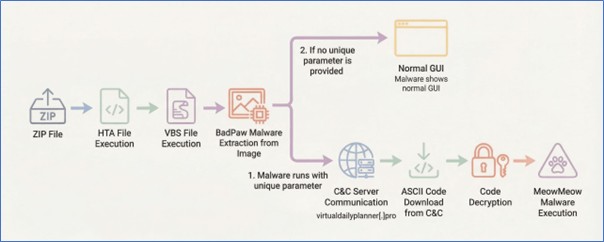
The attack chain initiates with a phishing email containing a link to a ZIP archive. Once
extracted, an initial HTA file displays a lure document written in Ukrainian concerning border
crossing appeals to deceive the victim. Simultaneously, the infection triggers the download of
BadPaw, a .NET-based loader. Upon establishing command-and-control (C2) communication,
the loader deploys MeowMeow, a sophisticated backdoor.
To hinder analysis and reverse engineering, both strains are obfuscated using the .NET Reactor packer, signaling a deliberate
effort by the threat actors to maintain persistence and evade detection.
To ensure persistence and evade discovery, both malware strains incorporate sophisticated
defense mechanisms.
The campaign employs strict Parameter Validation; the malicious
components remain dormant, running only “dummy” code with a benign GUI, unless executed
with specific, predefined parameters. Furthermore, the MeowMeow backdoor features
advanced environmental awareness. It actively scans for virtual machines and common
analysis tools such as Wireshark, ProcMon, and Fiddler, immediately terminating its execution
if a sandbox or researcher environment is detected.
ClearSky attributes this campaign with high confidence to a Russian state-aligned threat actor
and with low confidence to the specific group APT28 (Fancy Bear). This assessment is based
on a three-pronged analysis:
Targeting & Victimology: The focus on Ukrainian entities, combined with the
geopolitical nature of the lure, aligns with Russian strategic objectives.
Linguistic Artifacts: The presence of Russian-language strings within the code suggests
a development environment native to the region.
Tactical Overlap: The multi-stage infection chain, the use of .NET-based loaders, and
the specific obfuscation techniques mirror established tradecraft observed in previous
Russian cyber operations.
Read the full report: